Hello
Long time reader first time poster so bear with me.
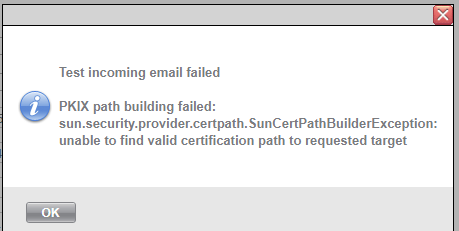
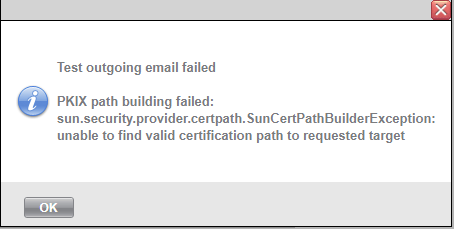
In my environment there is a legal need to scan every incoming and outgoing connection using our firewall (fortigate - deep ssl ) . The only functionality that is broken is no mail fetching due to ssl mismatch.
So my real question is : does the platform use different keystone than windows server root authority for outgoing connections ? I need to place my certificate somewhere, but all my tries were failed to say the least. Any ideas fellow sysaiders ?
(Have searched the docs , forums, to N/A)
Thank you